Data Breaches are inevitable
According to the European Commission, a data breach occurs when data under an organization's responsibility suffers a security incident that compromises its confidentiality, integrity, or availability.
Industry leaders and regulators now agree on a hard truth: on a long enough timeline, data breaches are inevitable.
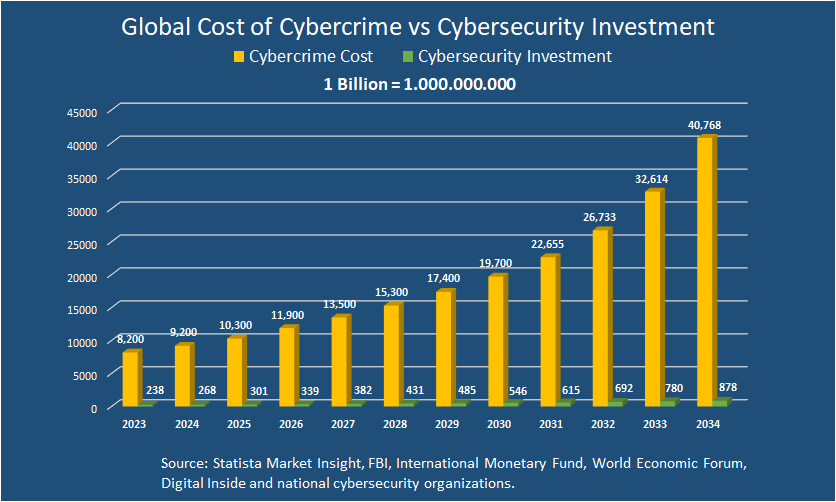
The IBM Cost of a Data Breach Report 2025 confirms that breaches occur despite strong preventive controls. As digital dependency grows, attacks become more frequent, more sophisticated, and more costly.
The question is no longer if your organization will be breached—but when, and how often.
As a result, cybersecurity strategy has shifted from pure prevention to resilience: detect faster, respond quicker, recover sooner.
But resilience has a critical blind spot.